Alot Solutions | SMS, WhatsApp, Voice & RCS APIs
Alot Solutions
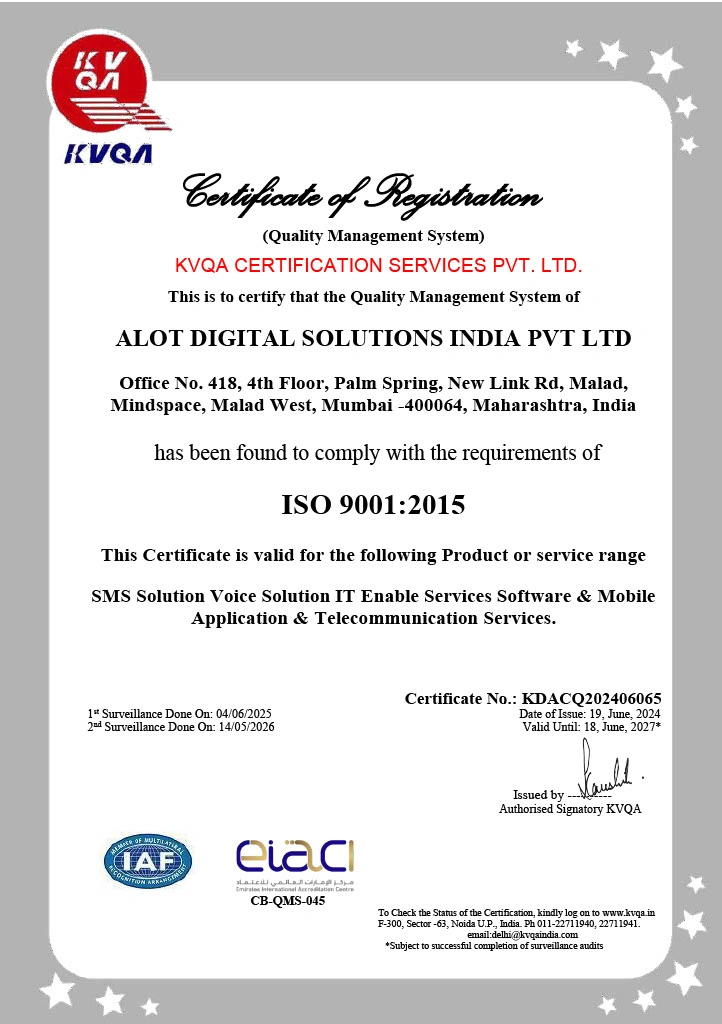
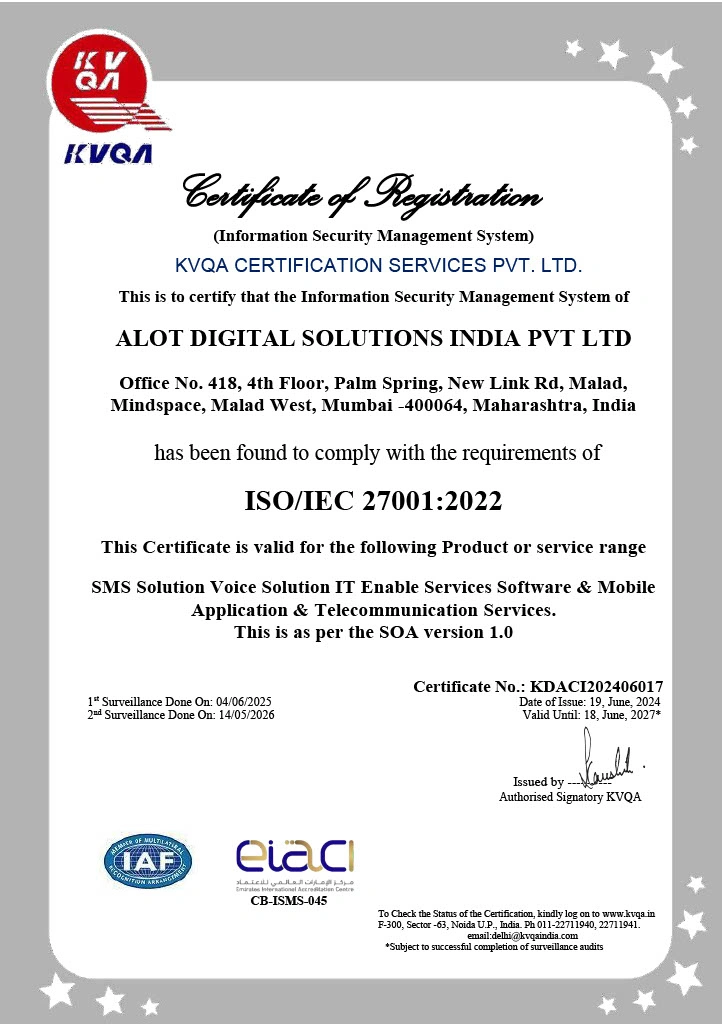
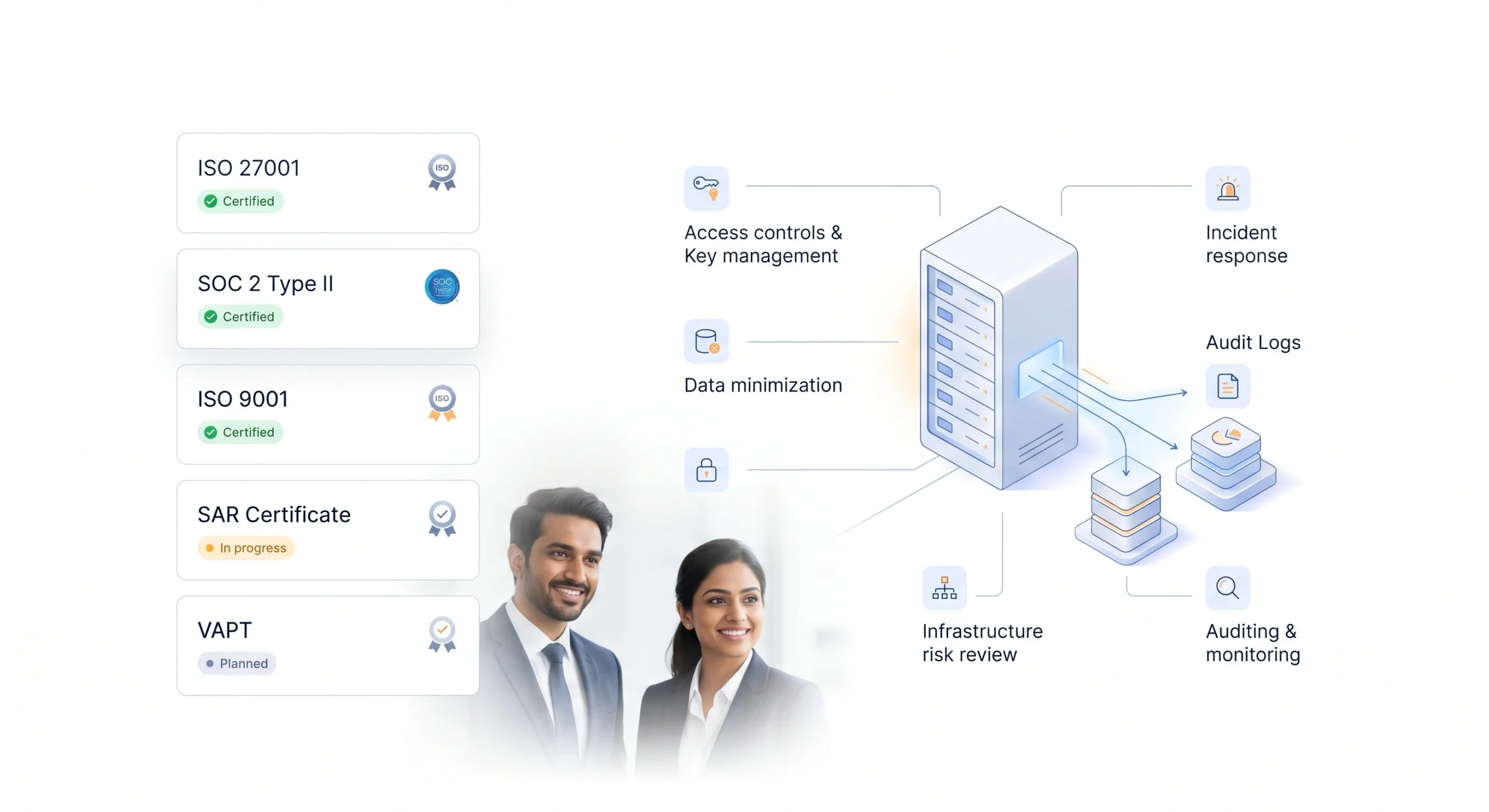
Certificates & Compliance
Security and privacy are core to how we operate. We follow best practices across access controls, auditing, monitoring, data handling, and incident response.
Access controls and secure key management
Data minimization and retention controls
Audit logs and delivery traceability
Vendor and infrastructure risk review
Incident response and operational monitoring
Certificates and Recognitions